Table of Contents
Introduction to the Mirai Attack
Cybersecurity threats are evolving rapidly. Some attacks become major turning points in internet history. One such example is the Mirai attack.
Mirai malware infected IoT devices like cameras, routers, and DVRs. It turned them into a botnet used to launch powerful DDoS attacks.
This incident showed how insecure IoT devices can be exploited. It also pushed organizations to improve cybersecurity.
What is the Mirai Botnet
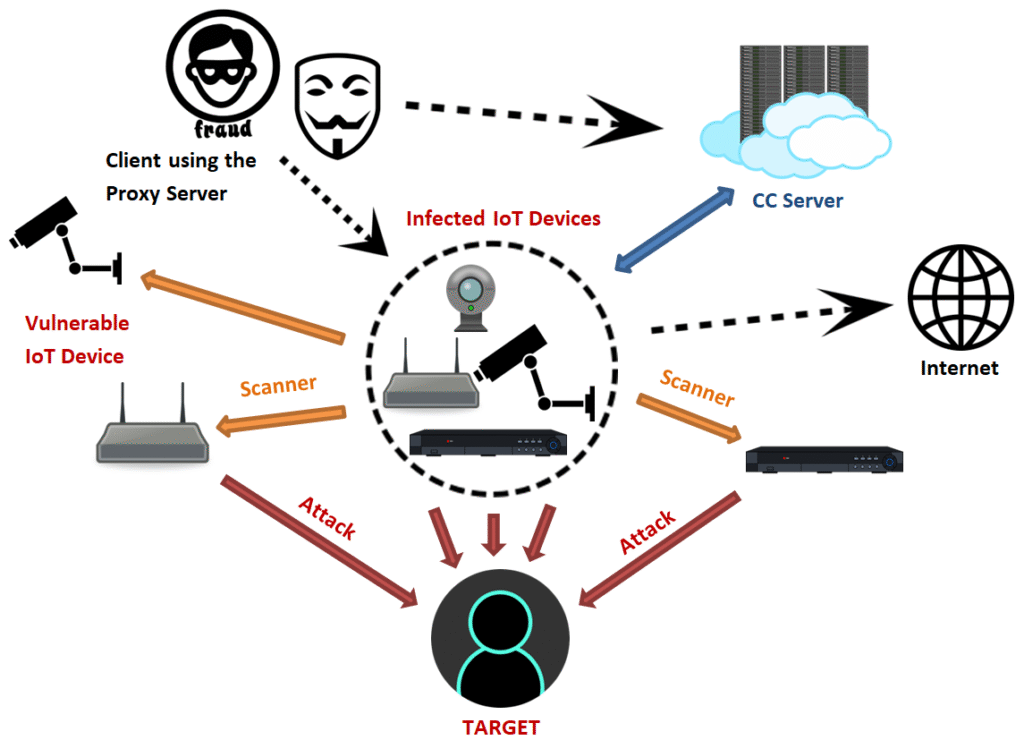
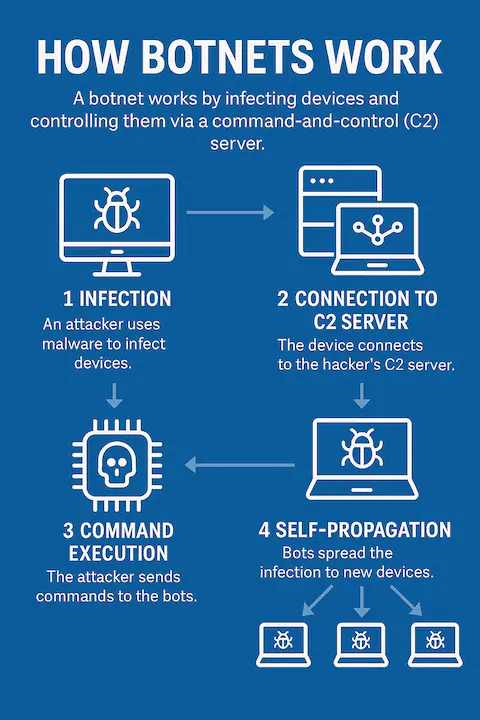
The Mirai botnet attack is malware that searches the internet for IoT devices using default usernames and passwords. It infects these devices and connects them to a command server controlled by attackers.
Unlike traditional malware, Mirai mainly targets smart devices that often lack security updates.
When many devices become infected, attackers can control them together to launch powerful cyberattacks. This is what makes Mirai so dangerous.
How the Mirai Attack Works
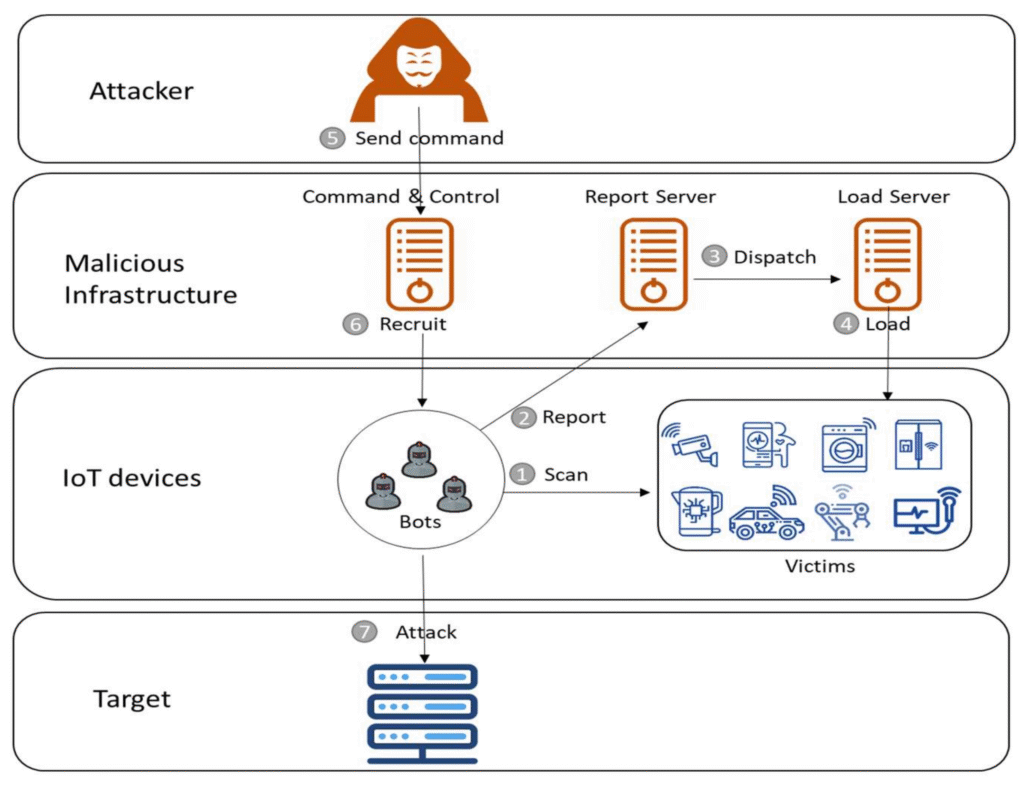
Mirai malware spreads by scanning the internet for devices with open ports and weak security. It logs in using common default usernames and passwords.
After gaining access, the malware installs itself and connects to a command server, turning the device into part of a botnet.
Attackers then use this botnet to send massive traffic to a target server, causing it to slow down or crash..
The Famous 2016 Internet Outage
Mirai attack scans the internet for devices with open ports and weak security. It logs in using common default usernames and passwords.
After gaining access, it connects the device to a command server and turns it into part of a botnet.
Attackers use this botnet to send massive traffic that can slow down or crash target servers.
Why IoT Devices Became Easy Targets
In the early days of IoT development, security was not considered a major priority. Many manufacturers focused more on convenience and competitive pricing rather than strong cybersecurity features. As a result, devices were often shipped with default usernames and passwords, and most users never changed them. In addition, firmware updates were either unavailable or rarely installed, which made these devices attractive targets for cybercriminals.
Another major issue was that many users did not realize their devices could be hacked. People usually associate hacking with computers or smartphones, but IoT devices operate quietly in the background, making it difficult to notice if they have been compromised. Weak authentication, lack of regular updates, and limited user awareness all played a significant role in the rapid spread of the Mirai malware.
Evolution of Mirai Variants
After the release of the original Mirai source code, cybercriminals began developing new and more advanced variants of the malware. These versions introduced improved scanning techniques, new methods of infection, and stronger attack capabilities. Some variants specifically targeted enterprise devices, while others were designed to focus on certain regions or types of networks. Because the source code was publicly available, even attackers with moderate technical knowledge were able to create their own botnets. As a result, IoT-based cyberattacks increased significantly around the world. Security researchers continue to analyze these variants to understand how they evolve and to develop effective ways to detect and prevent them.
How Organizations Can Defend Against Mirai Attacks
After the release of the original Mirai source code, cybercriminals began developing new and more advanced variants of the malware. These versions introduced improved scanning techniques, new methods of infection, and stronger attack capabilities. Some variants specifically targeted enterprise devices, while others were designed to focus on certain regions or types of networks. Because the source code was publicly available, even attackers with moderate technical knowledge were able to create their own botnets. As a result, IoT-based cyberattacks increased significantly around the world. Security researchers continue to analyze these variants to understand how they evolve and to develop effective ways to detect and prevent them.
Role of Ethical Hackers in Preventing IoT Botnets
One of the most effective ways to prevent cyberattacks is to ensure that IT professionals understand how hackers operate. For example, when security experts conduct penetration testing and vulnerability assessments, they can identify weaknesses not only in IoT devices but also across the entire network infrastructure. By using the insights gained from these security tests, organizations can strengthen their defenses and reduce the risk of large-scale attacks like Mirai in the future. In addition, ethical hackers play an important role in cybersecurity research by analyzing malware samples and developing tools that help detect and neutralize potential threats.
The Future of IoT Security
The number of smart devices is growing rapidly, making IoT security one of the most important concerns today. This trend is expected to continue for the next several years. To address these risks, device manufacturers are now implementing stronger security features such as secure boot processes, automatic firmware updates, and improved authentication methods.
However, challenges still remain because billions of IoT devices are already in use around the world, many of which lack proper security protections. The Mirai attack clearly showed why security must be a priority during the product design stage rather than something added later.
As technology continues to evolve, both businesses and individuals must stay aware of new cyber risks and take proactive steps to protect their digital environments using strong and updated security measures.
Conclusion
The Mirai incident was a major turning point in cybersecurity, especially when it comes to attacks on IoT devices. It revealed how vulnerable many smart devices were and how easily hackers could exploit them.
The attack also showed how cybercriminals could use these devices to disrupt major internet services. Because of this, it became a wake-up call for the technology industry, governments, and security professionals.
Even though cybersecurity has improved since then, similar threats can still happen. Understanding how Mirai works and applying strong security measures is important to protect today’s connected world.
